Understanding TACACS+
Terminal Access Controller Access Control System (TACACS+) is an Authentication, Authorization, and Accounting (AAA) protocol that is used for authenticating access to network devices, providing central authorization of operations and auditing of these operations. This protocol uses a client-server approach by which the client queries a server and the server replies with a pass or fail result for authentication. The communication between the client and server uses TCP as the transport protocol and requires a secret key.
You must configure the TACACS+ server before you can avail the TACACS+ functionalities on your network device. Netvisor ONE allows you to configure external TACACS+ servers for authentication, authorization, and accounting of sessions. You can configure any number of TACACS+ servers, and each server may be configured to handle any combination of authentication, session authorization, command authorization, session accounting, and command accounting.
Authentication, authorization, and accounting in Netvisor ONE have the attributes described below:
Authentication: Verifies the identity of the user through different authentication protocols with varying levels of security.
The authentication protocols supported by TACACS+ are:
- Password Authentication Protocol (PAP): The client must authenticate by providing the username and password during the establishment of a TACACS+ session. The password is sent to the TACACS+ server in cleartext.
- Challenge-Handshake Authentication Protocol (CHAP): A more secure authentication protocol that verifies the identity of the client periodically through a three-way handshake and uses a hashing algorithm for the password. Netvisor ONE uses CHAP authentication by default.
- Microsoft Challenge-Handshake Authentication Protocol (MS-CHAP ): Microsoft's version of CHAP that provides authenticator-controlled password change and authentication retry mechanisms.
Authorization: Gives fine-grained control over a TACACS+ session by stipulating the capabilities of the user. Authorization gives users a customized access to a device where they can be permitted or restricted in terms of using specific services.
Accounting: Keeps record of all the operations that a user performs while in an authorized TACACS+ session. TACACS+ supports three types of accounting messages based on the lifecycle of a service. These include messages indicating that a service is about to begin, a service is being performed, and a service is terminated.
Figure 17-1 illustrates a simple TACACS+ implementation.
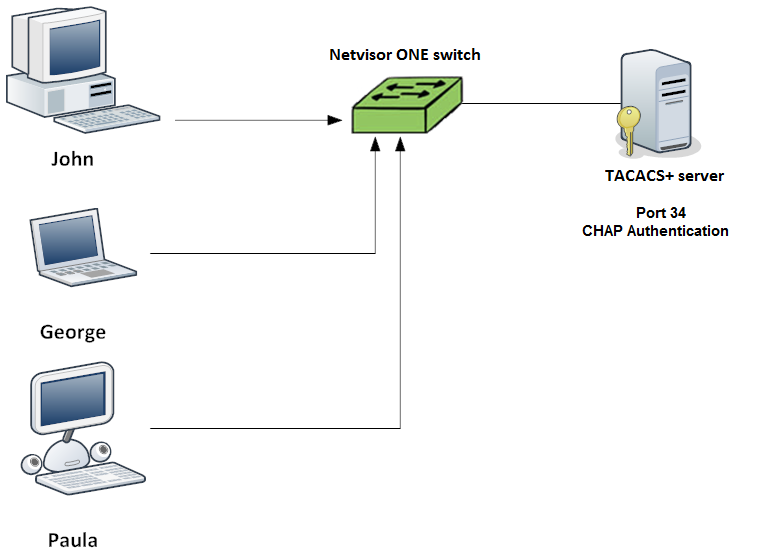
Figure 17-1: TACACS+ Implementation
