Using and Configuring IP ACLs
Configuring IP ACLs
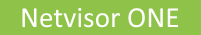
From Figure 13-4 Network Example - IP ACL for Internal Servers, the following information is available:
- Source IP address
- Source netmask
- Destination IP address
- Destination netmask
- Type of protocol to deny - IP
- Ports
- VLAN
Using a Deny IP ACL to Block Network Traffic
In this example, a network is shown with a Finance server on one part of the network, and an Engineering server on another part.
You want to block the Engineering server from the Finance server in order to protect company sensitive information.
See Configuring an Internal Deny ACL to review the configuration sample.
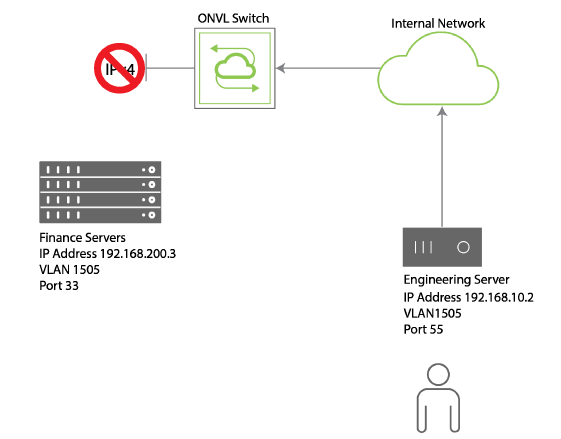
Figure 13-4 - Network Example - IP ACL for Internal Servers
Or, you may discover that an external source is attempting to access your network, and ping your servers for IP addresses.
You can use an ACL to block the specific source using an IP ACL.
Figure 13-5 - IP ACL Blocking External Access
See Configuring an External Deny ACL to review the configuration example.
Using IP ACLs to Allow Network Traffic
In the same manner, you can allow specific traffic to a destination such as the external server as shown in Figure 2 - IP ACL Blocking External Access.
To allow HTTP traffic to 209.225.113.24, see Configuring an External Allow IP ACL to review the configuration example.
Configuring an Internal Deny ACL
Let’s configure the ACL for denying traffic from the Engineering server to the Finance server and name the ACL, deny-finance:
CLI (network-admin@Leaf1) > acl-ip-create name deny-finance action deny scope local src-ip 192.168.10.2 src-ip-mask 24 dst-ip 192.168.200.3 dst-ip-netmask 24 proto ip src-port 55 dst-port 33 vlan 1505
To review the configuration, use the acl-ip-show command:
CLI (network-admin@Leaf1) > acl-ip-show name deny-hr layout vertical
name: deny-ip
id: b00011:20
action: deny
proto: ip
src-ip: 192.168.10.2/24
src-port: 55
dst-ip: 192.168.200.3/24
dst-port: 33
vlan: 1505
scope: local
port: 0
Now, when you attempt to access the Finance server from the Engineering server, the packets are dropped.
Configuring an External Deny ACL
From Figure 2 IP ACL Blocking External Access, you can see the following information:
- IP Address
- Port Number
To configure an ACL to deny traffic from the external server, use the acl-ip-create command to create an ACL named deny-external:
CLI (network-admin@Leaf1) > acl-ip-create name deny-external scope fabric src-ip 209.255.113.24/28
To review the configuration, use the acl-ip-show command:
CLI (network-admin@Leaf1) > acl-ip-show name deny-external layout vertical
name: deny-external
id: b000022:20
action: deny
proto: tcp
src-ip: 209.225.113.24/28
src-port: 0
dst-ip: ::/0
dst-port: 0
vlan: 0
scope: fabric
port: 0
Configuring an External Allow IP ACL
To allow HTTP traffic to the external server, 209.225.113.24 with a netmask of 255.255.255.240 and a scope of fabric, you can create an IP ACL called allow-http using the following syntax:
CLI (network-admin@Leaf1) > acl-ip-create name allow-http permit scope fabric src-ip 0.0.0.0. src-ip-mask 255.255.255.255 dst-ip 209.225.113.24 dst-ip-mask 255.255.255.240 protocol tcp dst-port 57
To review the configuration, use the acl-ip-show command:
CLI (network-admin@Leaf1) > >acl-ip-show name allow-http layout vertical
name: allow-http
id: b000025:20
action: allow
proto: tcp
src-ip: 0.0.0.0/255.255.255.255
src-port: 0
dst-ip: 209.225.113.24/28
dst-port: 57
vlan: 0
scope: fabric
port: 0
To delete the ACL configuration, use the acl-ip-delete command.
To modify the ACL configuration, use the acl-ip-modify command.
